
Introduction
Data and proactive insights garnered therein are vital strategic assets in the modern digital era. Amidst this backdrop, global regulations notably starting with the European Union (EU) Global Data Protection Regulation (GDPR) have become the vanguard to:
- Foster data privacy and sovereignty of individual citizens
- Define rigorous guidelines and best practices for data collection, storage, and use
- Mandate significant fines and penalties for entities in violation of data protection rules
It’s important to note too, that data sovereignty enables individual ownership of data and supports individuals to fully control how it is used while assuring that their data is protected in compliance with local regulations. Data sovereignty regulations require protection of personally identifiable information (PII) and limits access by unauthorized parties or entities and often mandates that resident PII be limited within the country’s geographical or international borders.
The rise of this concept has considerably raised the stakes for global companies as they need to comply with current and emerging privacy regulations and the dynamic macro environment across the geopolitical landscape. As the cloud is the de-facto hub of the digital world today, it adds a layer of complexity to these efforts as data used by companies may be hosted anywhere!
The business value of data protection
GDPR expects global enterprises who operate within the EU directly or have local business partners to ensure that the appropriate administrative, physical, and technical safeguards are deployed in the process of collecting, handling, and storage of personal data. As a result, GDPR has become the gold standard for data protection and has led other countries to promulgate rigorous local regulations for data protection and privacy.
The pace and velocity of data breaches, sophisticated attack pathways, and advanced persistent threats has significantly increased enterprise risk. This backdrop brings major challenges for data and privacy protection due to the dynamic and evolving regulatory environment.
Global companies face major fines and lawsuits for non-compliance or if they’re impacted by a breach. For example, GDPR penalties range from €20m up to 4% of worldwide revenue from the prior fiscal year. Lawsuits can be both regulatory and civil – so in effect “double jeopardy” is in play! There are also sectoral privacy regulations in the US, such as the Health Insurance Portability and Accountability Act (HIPAA) and state level regulations like the California Consumer Privacy Act.
Further, companies also risk reputation /brand impact, loss of business, and diverted management focus. Collectively, this has raised the table stakes for companies to bolster their data protection strategy and deploy state-of-the-art business processes, policies, training / awareness programs, and technology controls.
The modern cloud-centric digital era values data and actionable insights as a strategic business enabler to drive digital transformation, optimize costs, enhance productivity, and drive efficiency gains. The need for data protection and governance is mission critical. Data sovereignty principles and regulatory compliance mandates serve as “tail winds” to fuel these efforts.
A focus on data protection
Data protection across all data channels above requires safeguards for people, process and technology working in concert for regulatory compliance, breach protection, and enterprise risk minimization as detailed below.
- People: An Infosecurity Magazine report postulated that over 95% of data breaches were attributable to human error based on a study by Mimecast. Additionally, a study by the World Economic Forum also reported that 95% of all incidents could be traced to human error. Thus, both annual and periodic security and privacy training, as well as raising awareness, are mission critical. This can help bolster the “human firewall” as the first line of defense. This is especially important in this era of distributed work where employees work from anywhere via “anytime, anywhere authorized access.” Training can help reinforce best practices and secure user behavior as well as promote awareness about regulations and the impact of non-compliance.
- Process: Data classification policies and procedures developed and enacted by a cross-functional team of business stakeholders, and endorsed by the board or executive management, are fundamental to setting the tone for enterprise data protection. These should be complemented by business processes and data flow mapping to set a baseline for risk-based deployment of controls and protective technology strategies.
- Technology: There are multiple technological tools that are required to effectively enact holistic data protection, including but not limited to:
- Identity and access management: Identity is the cornerstone for secure delivery of digital applications and services. An identity and access management system that can deliver automated onboarding, offboarding, and empower employees with single sign-on via strong multi-factor authentication is essential. This can enhance productivity and minimize risk.
- Data characterization & governance platform: Characterizes data, identifies exposure risk, and performs remediation automatically. This is also an area wherein embedded artificial intelligence (AI) tools can power more effective and efficient management
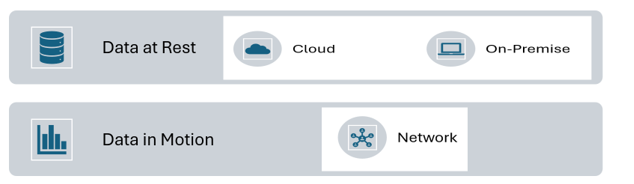
- Data loss prevention (DLP) is essential to protect data in motion and data at rest (DLP) via a state-of-the-art architecture
- Zero trust partners identity by changing security focus from network packets to users, applications, and data by dynamically evaluating user context / behavior, device posture and session risk. This assures secure access to mission critical data and applications regardless of location (zero trust network access –“ZTNA”)
- Cloud security is essential as the cloud is the hub of the modern digital era. Features such as network optimization; packet inspection and traffic management protect data in transit in addition to ZTNA
- Secure access service edge (SASE): A consolidated platform which combines a variety of security and networking applications / infrastructure and delivered via the cloud. It further reinforces identity & zero trust by protecting data, users, devices irrespective of geographical location by further rationalizing access and enhancing enterprise security.
- Note: ZTNA is one of the technologies considered as part of the SASE portfolio, in addition to cloud access security broker (CASB), firewall-as-a-service (FWaaS), software-defined wide area networking (SD-WAN) and secure web gateway (SWG).
Keep an eye out for my followup blog, coming out soon, which digs further into the future of digital trust and the evolution of data protection. In the meantime, if you’d like to learn more about data sovereignty, check out this episode of the Security Visionaries podcast with Michael Dickerson, who is helping to build Australia’s first indigenous sovereign cloud.




 Back
Back 





















 ブログを読む
ブログを読む