According to the Chinese zodiac, 2014 was the Year of the Horse. If Enterprise IT had a yearly zodiac, it would surely be the Year of the Cloud. Cloud computing has been front and center as an IT topic for well more than a decade, but 2014 in particular seemed to pick up more steam compared to recent years:
- IBM says cloud business enjoying breakthrough year
- Oracle jumps most in 6 years as cloud shift buoys results
- Microsoft earnings- cloud delivers growth again
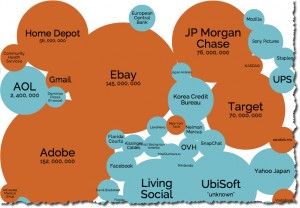
With the rash of well-publicized security breaches from Shellshock to Heartbleed, you might argue that security issues tempered cloud-computing momentum in 2014. The folks over at Information is Beautiful have a nice interactive visualization of the data breaches and hacks over the past decade and 2014 is chock-full of big events.
There are two forces that seem to be at odds here. Cloud growth appears to be exploding and at the same time, security breaches and hacks also appear to be on the rise. Is this is a matter of the more you increase use, the more vulnerable you will be? If only we had research to back this up. In fact we do! The Ponemon Institute recently conducted a Netskope-sponsored study, “Cloud Multiplier Effect On the Cost of a Data Breach” and found that IT folks believe that changing cloud app usage in the enterprise increases the probability of a data breach.
That takes us back to the original question. Did security issues temper cloud momentum in 2014? Perhaps cloud adoption could have grown even more if there were fewer security breaches? It looks like there are three options to limiting your exposure to security breaches.
Option#1 – Don’t use the cloud
Forego the cloud altogether and stick to on-premise. Block all your users from access to cloud services. Good luck competing in this world of elastic deployments and productive employees with anytime access to applications on any device. Besides, who is to say that on-premise is more secure? Security breaches and hacking is not limited to the cloud.
Option #2 – Use the cloud less
Given the findings in the Ponemon study, perhaps another option is to use the cloud in limited scope and only when absolutely necessary. The less you use it, the more secure you will be, right? This may be true, but once again, you are also reducing the potential value you are getting from cloud services. Besides, using the cloud less is actually very difficult in the Shadow IT era where your users are going to adopt the cloud regardless of what IT sanctions. Similar to option #1 you could perhaps block cloud applications for users, but once again, impacting user productivity is not a direction too many folks would recommend.
Option #3 – Use the cloud more, but better prepare and equip
What if you fully embrace the cloud, but limit your exposure to security issues by properly equipping yourself with solutions (www.netskope.com) that will help you move to the cloud safely? From identifying all cloud apps in use and understanding what the risk is to adopting fine-grained policy controls to ensure that data and usage is secure. Don’t block all cloud apps, only the ones that are risky and perhaps only certain activities and certain content types and maybe on certain devices. You get to have your cake (the cloud) and eat it too (limit security risk).
Speaking of better preparing yourself when adopting the cloud, Netskope’s quarterly cloud reports in 2014 unveiled some interesting stats around cloud usage. This data could be useful in helping you properly prepare for your cloud deployments. Below is a summary of the key findings in 2014 along with links to each report.
2014 Cloud Report Findings
- Cloud adoption climbed from 397 cloud apps per enterprise at the beginning of the year to 579 apps at the end of the year
- Enterprises use 10 times the number of cloud apps than IT thinks they do
- More than 88% of cloud apps are not enterprise-ready
- More than 90% of organizations admit losing control of sensitive content in cloud file-sharing apps
- There are three shares for every one upload in cloud storage apps
- More than one-third of all cloud data leakage policy violations occur on mobile devices
- Download, edit, and upload are among top 5 policy violations in cloud apps, pointing to both concerns over data leakage and compliance
Netskope Cloud Reports – 2014
January 2014 – Reality vs. Perception: More Cloud Apps Than You Realize
April 2014 – Upload and Edit are Most Common Causes of Policy Violations




 Voltar
Voltar 















 Leia o Blog
Leia o Blog