Attackers were quick to exploit the COVID-19 pandemic, with coronavirus-themed phishing campaigns, Trojans delivering ransomware and backdoors, and other scams. Netskope Threat Labs have been keeping a close eye on the threat landscape and tracking COVID-related campaigns throughout this unprecedented time.
This blog post details a COVID-19 relief package scam that has been active since April 2020. The attacker has recently registered new domains from which they are hosting the scam. The attacker’s use of social media—leveraging victims to actively share the scam with their contacts—has contributed to the scam’s longevity. Every version of the scam is based on the same template, helping the attacker to pivot to new cloud services and hosting providers when necessary. The attacker behind this campaign has hosted multiple similar scams, each targeting victims in specific countries, with some of its infrastructure hosted in Google’s Blogger service on blogspot.com. This post provides a breakdown of the scam and the blogger profiles behind it.
Background
During August 2020, Netskope Threat Labs discovered two newly registered domains—https://fundzforcovid19[.]com and https://fundsforcovid19[.]com—being shared in WhatsApp messages. Both the websites presented a fake Government Lockdown Funds page as shown in Figure 1.
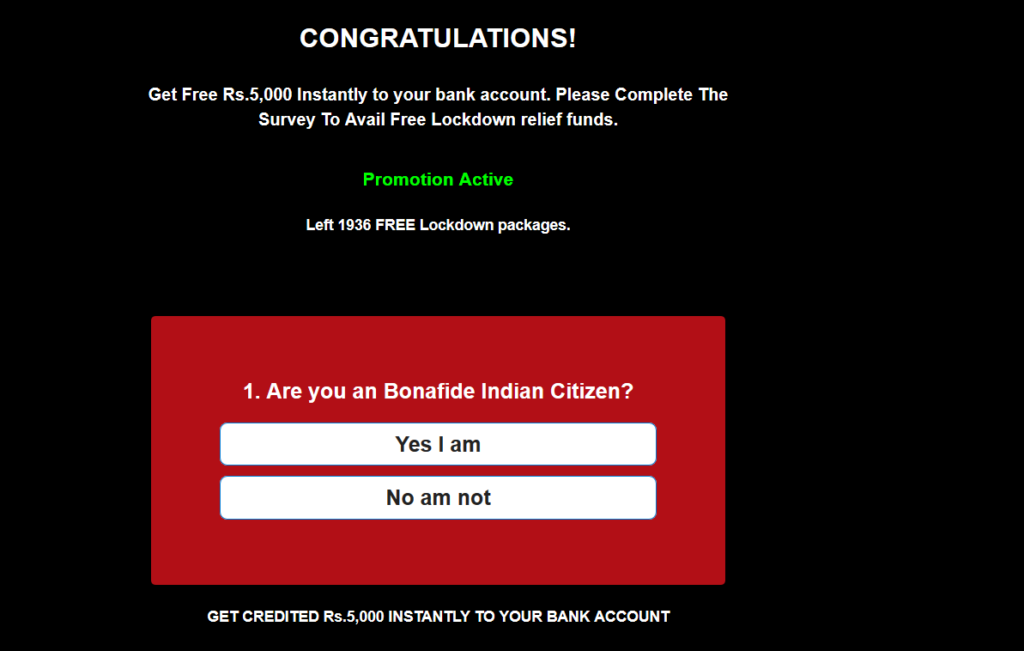
The webpage shared similarities to the news published by The Quint in May 2020: a viral message floating around on WhatsApp claiming that the government is giving a “free” relief fund of Rs 5,000 to each Indian citizen amid the coronavirus lockdown.
During our analysis, we discovered this scam was also being spread through Facebook, and that the attackers responsible have launched similar variants targeting victims in different countries, including Egypt, Ghana, India, Kenya, Malaysia, Nigeria, South Africa, and Uganda.
We tied these attacks together based on the template and a profile hosting scam pages in Google’s Blogger service on blogspot.com.
Analysis
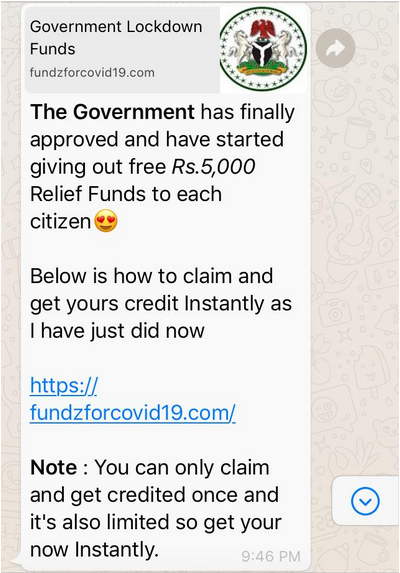
The longevity of this scam can be attributed to its use of social media. It is primarily distributed via forwards on Facebook and WhatsApp, like the message shown in Figure 2. In the week before posting this blog, I myself received messages like this from 10 different contacts in WhatsApp.
Upon visiting the website, https://fundzforcovid19[.]com, the victim is presented with a Government Lockdown Funds page with this message, “This offer is limited only till 2 25th of August .. Hurry!! So far 105314 users have received their Rs.5,000 Lockdown.” The message contained a typo, “till 2 25th August,” and the user’s number was incrementally randomized with a counter timer. The date is static, indicating the attacker will likely alter the text after the 25th passes.
The victim then fills out a short questionnaire and is prompted to share the message to WhatsApp groups using the “Share Now” option to claim the money as shown in Figure 3.
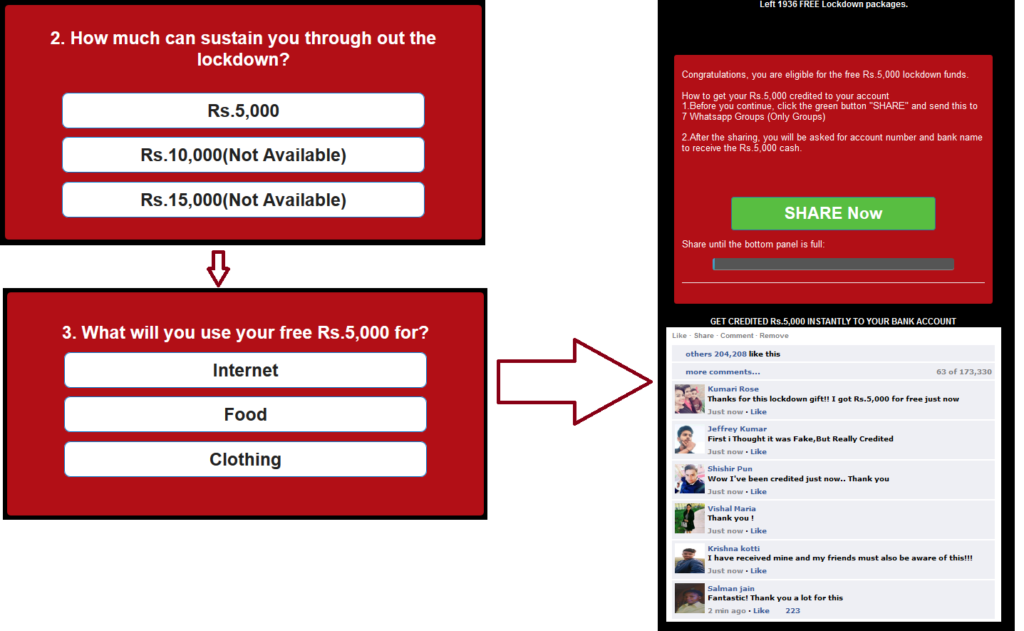
The page also displays fake Facebook messages that users have received the money in their bank account. This message has to be shared across WhatsApp groups to receive the cash, thus continuing the spread of this scam
The sharing is invoked via the function var walink = “whatsapp://send?text=”+WhatsApp_share_message+Share_link. Upon sharing more than 9 times, the victim is presented with another webpage, https://fundsforcovid19[.]com/2.html?, as shown in Figure 4.
![Screenshot showing code redirecting victim to https://fundsforcovid19[.]com/2.html?](https://www.netskope.com/wp-content/uploads/2020/08/Blogspot-5-1024x643.png)
On visiting the new website, the victim is presented with a message to input the account number and the bank as shown in Figure 5.
![Screenshot showing message displayed on visiting https://fundsforcovid19[.]com/2.html?](https://www.netskope.com/wp-content/uploads/2020/08/Blogspot-6-1024x521.png)
On entering the details and clicking on the “Claim Now” option, the victim is directed to the website, http://itnuzleafan[.]com/4/3317123, which serves up unwanted ads but does not store the victim’s credentials. The scam appears to be solely to collect ad revenue and not to phish for bank account numbers.
Attacker’s details in the webpages
We discovered 42 similar scam themes targeting different regions and identified two interesting details in the source of the webpage.
The first one was the usage of the Google Forms page in the website for people who wanted to buy the script used in the scam as shown in Figure 6.
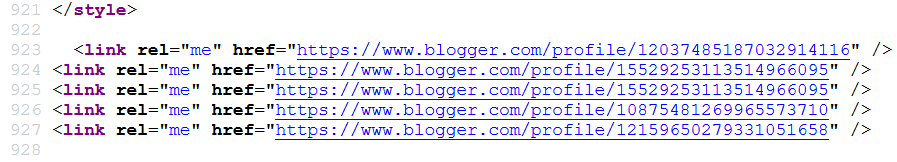
Upon visiting the profiles, we identified the blogger profile, https://www.blogger[.]com/profile/12159650279331051658, hosted multiple similar scams as shown in Figure 7.
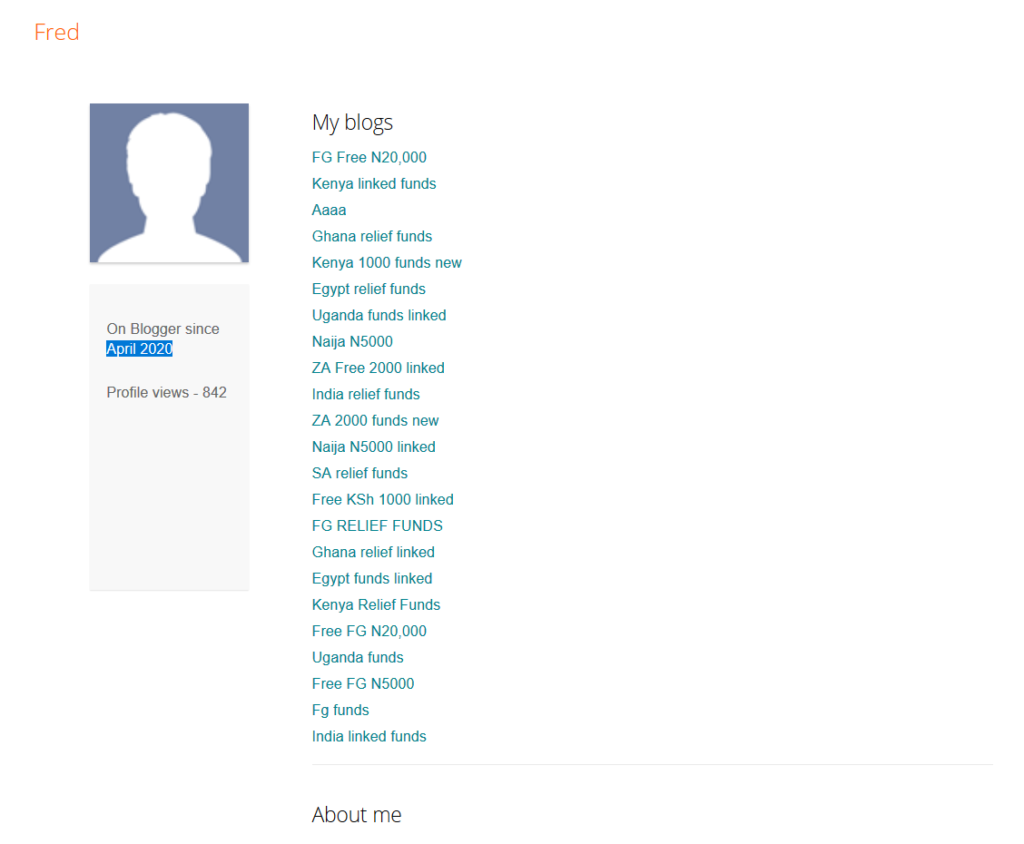
At the time of analysis, the profile contained 23 scam links with a majority of them posing as a COVID-19 lockdown relief package. The profile has been active since April 2020 which suggests that the scam operation likely started at that time.
As the webpages are hosted in blogspot[.]com they carried a trusted certificate verified from Google Trust services. The other non-blogger domains had valid SSL certificates issued by LetsEncrypt. Alongside this, none of the websites were detected or blocked by security scanning services in popular browsers like Chrome and Firefox.
Conclusion
Attackers are always on the hunt taking advantage of the news with high media attention as lures. The COVID-19 relief package scam is a classic example. Alongside this, scams and phishing campaigns are using cloud services to evade blocklists and appear legitimate (also covered in our previous work on Old Scams Getting New Life in the Cloud). Users should be able to recognize the services commonly used for these scams and be wary of messages shared through social media and instead look for official government communication for authenticity. Netskope reported the phishing sites to the Blogger Security team and also notified WhatsApp about this scam on August 19, 2020.
IOCs
https://fundsforcovid19[.]com
https://fundzforcovid19[.]com
https://myr.ngodataz[.]com
https://india-relieef.blogspot[.]com
https://india-relief-funds.blogspot[.]com
https://fund.ramaphosafoundations[.]com
https://relieffund.freeinternetz[.]com
https://covid19-relief-fund.ngodataz[.]com
https://india-fundds.blogspot[.]com
https://india-fnd.blogspot[.]com
https://bigoffer[.]in
https://freeinternetdata[.]com
https://freemobiledata[.]xyz
https://durbanvideos[.]com
https://ramaphosaorganization[.]xyz
https://freemobiledataz[.]com
https://ramaphosacyrilfoundation[.]com
https://bestngodataz[.]com
https://covid19-relief-fund[.]com
https://free-fgn-funds.blogspot[.]com
https://fg-ksh-funds.blogspot[.]com
https://dfyfgg.blogspot[.]com
https://fg-free-ghs.blogspot[.]com
https://ksh-funds.blogspot[.]com
https://free-egp-funds.blogspot[.]com
https://ug-fund.blogspot[.]com
https://ng-funds.blogspot[.]com
https://za-free-funds.blogspot[.]com
https://free-fg-rupees.blogspot[.]com
https://za-free-fund.blogspot[.]com
https://ng-fund.blogspot[.]com
https://free-relief-funds.blogspot[.]com
https://fg-free-kshfunds.blogspot[.]com
https://fg-relief-funds.blogspot[.]com
https://free-ghs-funds.blogspot[.]com
https://fg-free-egp.blogspot[.]com
https://free-ksh-funds.blogspot[.]com
https://free-fgn-fund.blogspot[.]com
https://ug-funds.blogspot[.]com
https://free-fg-n5000.blogspot[.]com
https://fg-free-fund.blogspot[.]com
https://fg-free-rs.blogspot[.]com
https://www.blogger[.]com/profile/12159650279331051658




 Zurück
Zurück 





















 Den Blog lesen
Den Blog lesen